Today’s post is not about SQL Server, but if you’re working in Azure from a dynamic IP address, you might still find it useful.
Recently, my home ISP has started changing my public IP address. This causes me some headache because I have a couple of Azure Network Security Group rules (think of them as firewall rules) that specifically allow my home IP access to all of my Azure resources. When my home IP changes, those rules have to be updated accordingly.
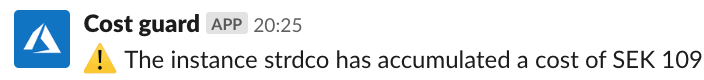
So I made a PowerShell-based solution to automatically maintain them.